|
CSCtl96208
|
"capwap ap hostname" CLI returns "ERROR!!! Command is disabled."
|
|
CSCuf77488
|
wips alarm detection time stamp is ahead of AP clock
|
|
CSCui95938
|
fast Switching SSDi and IPAD Issue
|
|
CSCul42704
|
WIPS-Rogue APs are mistaken as infrastructure devices
|
|
CSCun06894
|
duplicate mac address issue of Ap Rcv image
|
|
CSCun52472
|
"show dtls connection" shows blank in AP Name column for Capwap_Data
|
|
CSCuo16301
|
HA:-Unable to pair up the active/Standby wlc due to config sync failure.
|
|
CSCuo19601
|
Flex AP in Standalone mode not triggering ap-primed-join-timeout timer
|
|
CSCuo48442
|
Stale old DTLS data_encryption session histories are left on WLC
|
|
CSCup13091
|
Local eap, local user, created for specific WLAN works for diferent wlan
|
|
CSCup64468
|
WLC device sends invalid format "#" in front of syslog message
|
|
CSCup68372
|
Stats are carried over when session timeout occurs
|
|
CSCup72502
|
5500 on 7.6 does not deauth client when Flex ACL is not present on AP
|
|
CSCup75446
|
Default interface takes precedence over foreign VLAN mapping with CWA
|
|
CSCup80403
|
Low iMac Tput -supported rate IE in association response has ZERO length
|
|
CSCuq50069
|
SHA1 key cipher not working between WLC 80 and MSE 80 CCO versions.
|
|
CSCuq68753
|
5500 anchor running 7.6.122.21 crashed on osapiBsnTimer
|
|
CSCuq73590
|
WLC adds incorrect class attribute in accounting stop
|
|
CSCuq88748
|
Rogue APs wrong classification from malicious to unclassified
|
|
CSCur13400
|
DHCP Option 82 and Sub Option 5 issue in WLC 8.0
|
|
CSCur25239
|
Controller crash on mping command over telnet/ssh
|
|
CSCur32475
|
NewMobility Web-Auth on MacFilter Failure always send client to web-auth
|
|
CSCur43124
|
WSSI module stops working after Upgrade from 7.4.121.0 to 7.6 MR3
|
|
CSCur48612
|
8.1 emWeb crash when adding devices to mDNS policy
|
|
CSCur48944
|
Problem in Client Stats Reports and Optimized Roaming
|
|
CSCur49165
|
WiSM2 system crash radiusTransportThread aaaRadiusAuth
|
|
CSCur57909
|
Client misses to override vlan after shifting wlan.
|
|
CSCur60218
|
New mobility web auth on mac filter failure Export Anchor request fails
|
|
CSCur74208
|
Name/OID: cLMobilityExtMgrAddress.0; Returning in IP in Reverse Order
|
|
CSCur80935
|
8.0.100.0:AAA overridden acl is not applied on Guest access controller
|
|
CSCur88307
|
AP name unknown in dissoc messages (Intermittent)
|
|
CSCur90555
|
T8.0 WLC keeps ghost client entry
|
|
CSCur91936
|
MDNS discovery issue with WLC 8.0.100
|
|
CSCur95365
|
Controller crashes when issuing command show ap config general
|
|
CSCus03406
|
Dataplane crash on 8500 WLC with 7.6
|
|
CSCus07013
|
Adding mac filter check when client is changing SSID for webauth
|
|
CSCus20991
|
Radius NAC Client auth issues for 7.6.130.0
|
|
CSCus30429
|
OEAP600 not giving ip on remote LAN port in 8.0
|
|
CSCus33759
|
Local Policies not working after OUI Update
|
|
CSCus51456
|
WLC - Radius multiple UDP source port support for radius protocol
|
|
CSCus53635
|
Add 802.11a Philipines country support for 1532I Aps joined to 5760.
|
|
CSCus61445
|
DNS ACL on wlc is not working - AP not Send DTLS to WLC
|
|
CSCus68340
|
Standby keeps auto rebooting and stays in "STANDBY COLD" state
|
|
CSCus73932
|
Multicast configuration issue on 8510 WLC OS 8.0.110.4
|
|
CSCus74299
|
New mobility:Client not deleted on 5508 when it roams at webauth state
|
|
CSCus74362
|
controller crashed with task radiusTransportThread
|
|
CSCus76833
|
CT5508 crashes at sisfSwitcherTask
|
|
CSCus77368
|
WLC: Crash ewaFormSubmit_cell_edit
|
|
CSCus80478
|
CAP1530 not forward, send packets to wired side after bootup
|
|
CSCus80685
|
AP sends few frames with previous security association's packet number
|
|
CSCus89468
|
Need to add AP802 to list of APs that support Flex+Bridge mode
|
|
CSCus91439
|
WLC - Memory leak - k_mib_cisco_lwapp_dot11_client.c
|
|
CSCut02524
|
default NAS-ID value at the AP-Groups should be empty or "none"
|
|
CSCut09821
|
Unused Data DTLS session is remained on WLC running 7.6.130.19
|
|
CSCut14459
|
session ID changes for an intercontroller client roam using EAPFAST
|
|
CSCut16170
|
Mobility tunnel down after switchover on 7.6
|
|
CSCut25670
|
CSCuwAP: %DTLS-5-SEND_ALERT: Send FATAL; join failure loop
|
|
CSCut27598
|
Client unable to get IP when switching wlan on New mobility.
|
|
CSCut31468
|
local profile showing wrong stats under Manufacturer Stats
|
|
CSCut39118
|
WLC 8510 Failure to collect feature MobilityExtGroupMember on PI 2.2
|
|
CSCut42926
|
WLC crash on SNMPtask after doing config audit from PI
|
|
CSCut43770
|
PMIPv6 Client Traffic is Sent to the Wrong LMA
|
|
CSCut62319
|
Broadcast Key Rotation won't occur after MAC Filtering enabled
|
|
CSCut70403
|
Jian WLC crashed with task name 'HAConfigSyncTask'
|
|
CSCut74263
|
MAG on AP:AP does not clear bindings after session/user timeout & deauth
|
|
CSCut76481
|
WLC sends 1499 bytes MTU switchover
|
|
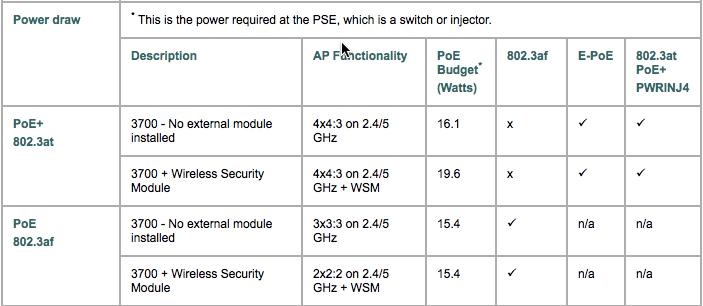
CSCut87326
|
WLC generates SNMP traps to PI 2.2 for AIR-3702 PoE+ getting low power
|
|
CSCut93569
|
MSE - NMSP inactive with WLC
|
|
CSCut93712
|
AP not send RM IE for 11k in association response; no 11k for iOS > 8.1
|
|
CSCut97683
|
WLC crash on spamApTask2 8.0.110.0
|
|
CSCut99150
|
2702 AP requesting as a Type 1 power device instead of Type 2
|
|
CSCuu06047
|
Packet drops on 2702 AP in flex local auth/local switch mode
|
|
CSCuu07700
|
EAP Packet does not get encrypted in Re-auth request from client
|
|
CSCuu08752
|
SXP Crash when running Trust Sec clients on Talwar
|
|
CSCuu20097
|
Token Bucket leak when QoS Roles setup and when working with WebAuth
|
|
CSCuu37437
|
WLC8510 crashing while NMSP polling in progress.
|
|
CSCuu45186
|
dot11 arp-cache does not works well
|
|
CSCuu47016
|
Cisco Application Visibility and Control UDP Vulnerability
|
|
CSCuu49291
|
7925 decrypt errors with AP1131 running 8.0 code
|
|
CSCuu54100
|
Switching between SSIDs fails with FAST SSID enabled on PMIPv6 WLANs
|
|
CSCuu59589
|
False positive AP sourced AP impersonation on corrupted beacon
|
|
CSCuu66675
|
Lock crash on radiusTransportThread during CMCC external auth
|
|
CSCuu68490
|
duplicate radius-acct update message sent while roaming
|
|
CSCuu72366
|
Silent Crash 8.0.110.11 mmListen process
|
|
CSCuu77304
|
Clients deauthenticated from OEAP 600 LAN ports
|
|
CSCuu82416
|
Evaluation of wlc for OpenSSL June 2015
|
|
CSCuu83748
|
WLC sends bsnRogueAPRemoved Trap when notify configured none
|
|
CSCuu83941
|
8510: Error enabling global multicast with capwap mode unicast
|
|
CSCuu91001
|
Netflow record sent without client IP address
|
|
CSCuu93296
|
EAP-TLS loosing device certificate in standalone mode after reboot
|
|
CSCuu98792
|
AP 1570, antenna enable config is lost on reboot
|
|
CSCuu99344
|
WLC crash - DHCP packet content while on new mobility
|
|
CSCuv00107
|
PMIPv6 Client MAC Address shows up on the mac address table of Switch
|
|
CSCuv00598
|
Optimized Roaming per WLAN feature
|
|
CSCuv04474
|
Sanity: AP1700 crashed during multicast client traffic(cont.CSCuu89311)
|
|
CSCuv09655
|
Anchor crash on 8.0.110.14 New Mobility apf_msDeleteTblEntry
|
|
CSCuv13731
|
3702 AP sends burst traffic - AMPU/MSDU/Off-channel/RRM disabled
|
|
CSCuv22052
|
Link local multicast control traffic sent by APs, IGMP Snooping Enabled
|
|
CSCuv27320
|
Wired clients in 702w AP leaking traffic across ports/vlans
|
|
CSCuv28555
|
3702 - Voice Queue stuck, with no new clients able to associate.
|
|
CSCuv31162
|
WLC 5500 Crashes continously in HA Setup@task: apfRogueTask_2 and 3
|
|
CSCuv34277
|
Wireless Client not able to get IP address on 3650 MA from 5508 anchor
|
|
CSCuv34946
|
EOGRE and PMIPv6 client fails to move to Run state
|
|
CSCuv36505
|
8.0 WLC messages flooding cli after debug client
|
|
CSCuv37613
|
Apple devices failing 802.11r FT roam
|
|
CSCuv51521
|
Active WLC should send GARPs when HA Re-Paring after Active-Active state
|
|
CSCuv53952
|
SSID still broadcasted by the AP after the wlan is deleted from wlc
|
|
CSCuv61271
|
Window DHCP BAD_ADDRESS for Access Points
|
|
CSCuv67144
|
Need to re-evaludate Algeria if in -E or -I
|
|
CSCuv69967
|
OEAP600 wired 802.1x remote LAN forward traffic in 802.1x Required State
|
|
CSCuv82110
|
vWLC: Decrypt errors occurred for client using WPA2 key on 802.11a intf
|
|
CSCuv85747
|
Mobility Member entries going stale
|
|
CSCuv86494
|
WLC clears AP MAC before deleting client, sends netflow with Zero AP MAC
|
|
CSCuv87657
|
8.0/8.1 WLC's fail to send FRAMED-IP attribute to AAA server
|
|
CSCuv87839
|
Wired clients in 702w AP getting put in mgmt vlan
|
|
CSCuv90333
|
Pineridge - afpmsConntask flood when running client console debug
|
|
CSCuv96333
|
readonly user able to change "Telnet Capability" setting
|
|
CSCuv97793
|
WiSM2 crash AP_DB_CREATE_ERR Message queue MFP-Q is nearing full
|
|
CSCuw03414
|
WLC crash: "Software Failed while accessing the data"
|
|
CSCuw06127
|
Silent crash 8.0.120 due to memory leak in CDP Main
|
|
CSCuw06153
|
unauthorized configuration change for web management
|
|
CSCuw10610
|
Non authenticated HTTP page allows to logout any connected client
|
|
CSCuw12544
|
Rate-limiting is causing 500ms gap of traffic when roaming
|
|
CSCuw13264
|
702w missing interface information on controller after HA failover
|
|
CSCuw15008
|
Mobility Task Hogs CPU - Reaper Reset in SpamApTask
|
|
CSCuw24476
|
Increased Ping latency & Reduced traffic on 8510 with QOS rate limiting
|
|
CSCuw26377
|
Crash due to invalid form field validation on switch_cfg_rw.html
|
|
CSCuw29419
|
Cisco Wireless LAN Controller Radius Packet of Disconnect Vulnerability
|
|
CSCuw29564
|
APs show 0 neighbors on 5GHz band and client 802.11 packets are ignored
|
|
CSCuw35341
|
IP address lost on AAA override+muiltiple subnetworks per vlan+DHCP req
|
|
CSCuw35349
|
DHCP registration failing when mask from WLC intf does not match client received mask
|
|
CSCuw44480
|
802.11r client fails auth if self reset before user idle timeout expires
|
|
CSCuw50324
|
Crash on high CPU for bonjour
|
|
CSCuw57588
|
C3600 AP crash on am_xml_GetChildCount
|
|
CSCuw87468
|
Rogue containment not working on 8.0.120.0 for AP3700 with WSM module
|
|
CSCuw89581
|
WLC System Crash on apfReceiveTask
|
|
CSCuw90625
|
Rogue rules not applied correctly after upgrade to 7.6.130.30
|
|
CSCuw91763
|
Feature "AES Key Wrap" does not work
|
|
CSCux03108
|
8510 crashed on Task Name:portalMsgTask.
|
|
CSCux18259
|
PI 3.0 - Sync Issue on Flexconnect Native VLAN Configuration
|
|
CSCux41354
|
Evaluation of wlc for OpenSSL December 2015 vulnerabilities
|
|
CSCux47470
|
8.0.110.14 controller crash at openssl_cert_hash_algo_check_callback
|
|
CSCux22935
|
HA+802.11r:Post SSO FT PSK/EAP Apple clients fails to connect.
|
|
CSCux22620
|
8510 WLC crash in radiusTransportThread system task
|
|
CSCut23325
|
1700 AP not encrypting icmp and arp sent from the client over the air
|
|
CSCus92667
|
GET on Ap groups Table after set - response missing
|
|
CSCus39396
|
8.0.100.0 QoS Bronze Profile not marking traffic to AF11 on Flex
|
|
CSCut06502
|
WLC crash due to task name RRM-CLNT-5_0
|
|
CSCut48172
|
LSC AP provisioning happening after MAP is disconnected for long time
|
|
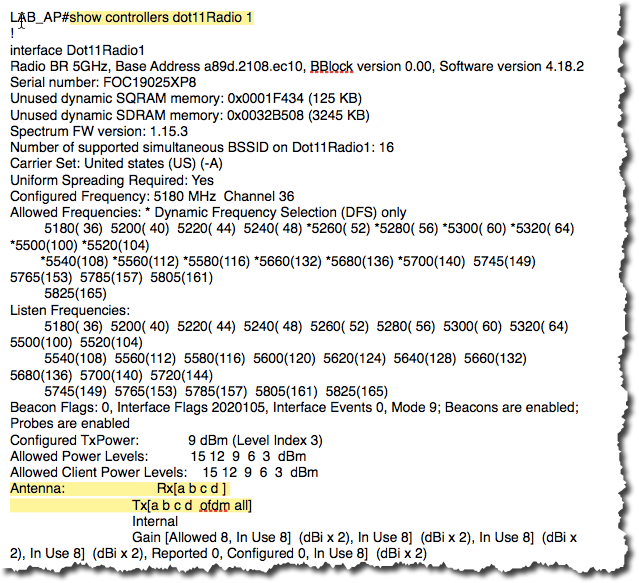
CSCtu45614
|
Spectrum Management Bit Should be set to 1 all the time
|
 Tuesday, April 19, 2016 at 2:12PM
Tuesday, April 19, 2016 at 2:12PM