First, this is a lot of information and it is very detailed at that. I encourage further reading and study for a complete step by step explanation. These are my notes for reference. I hope you find them useful.
If you are new to wireless security especially 802.11i, one could be intimidated by all of these KEYS. I can remember thinking to myself, “Why in gods name is there so many keys and they do what again!?”
I would encourage you to read Chapter 5 of the official CWSP study guide, Devin’s ‘chicken egg’ white paper and the 802.11 Wireless Networks ‘Definitive Guide 2nd edition’ for a full explanation.
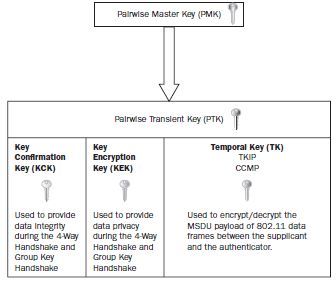
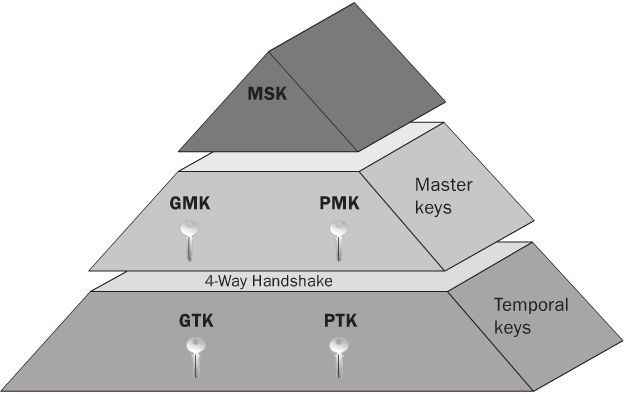
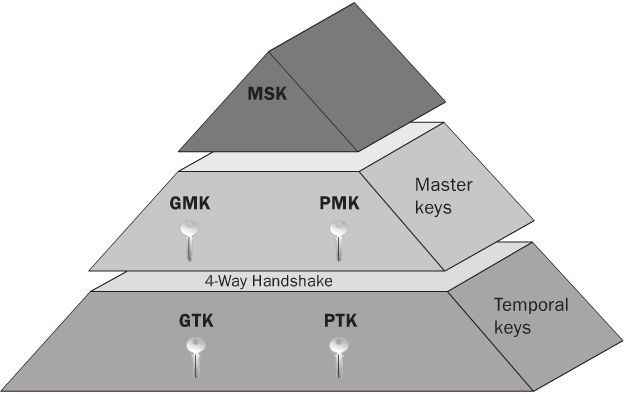
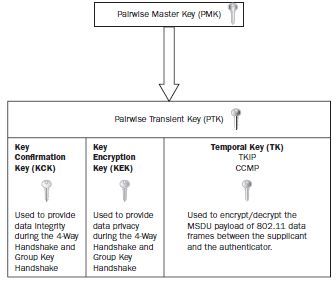
To simplify, I would like to reference fig 5.18 on page 194 of the CWSP study guide. The pyramid offers a great visual as to the RSN Key Hierarchy process. Let’s break down each LAYER.
“Master Session Key - MSK”
The MSK is sometimes called the ‘AAA key’. The MSK is on top of the food chain and will provide “seeding / keying material” for the PMK (Pairwise Master Key). MSKs are created during the 802.1X/EAP process.
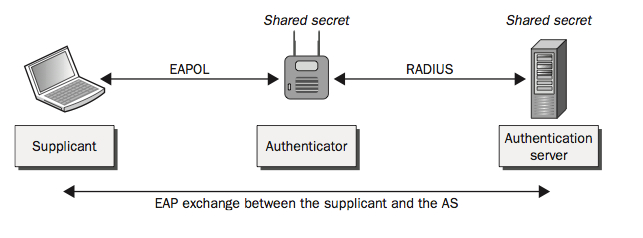
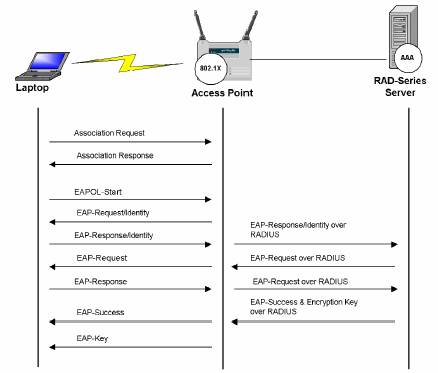
802.1X/EAP – The MSK is derived at the supplicant and the authentication server (AAA) during the EAP authentication process. The supplicant and the authentication server (AAA) will know information about each other during the “mutual” authentication exchange of credentials. I added a GREAT Peap Choreography at the end of this post.
(this is all black magic and is outside of the scope of the exam)
What is important to remember is that both the supplicant and authentication server (AAA) have both derived identical MSK keys during this mutual authentication process which will later be used as seeding material for PMKs.
PSK - In the case where PSK is used, whereby putting a static PSK key on a station and access point there is no MSK keying material because there is no authentication server (AAA) in use to derive a MSK. So your PSK is your PMK.
Additional reading material
<RFC4017 states>
Master Session Key (MSK) Keying material that is derived between the EAP peer and server and exported by the EAP
method. The MSK is at least 64 octets in length. In existing implementations, an AAA server acting as an EAP server
transports the MSK to the authenticator.
<802.11 2007 states:>
3.80 master session key (MSK): Keying material that is derived between the Extensible Authentication Protocol (EAP) peer and
exported by the EAP method to the Authentication Server (AS). This key is at least 64 octets in length.
“Master Key Layer”
Next layer down on the food chain is the “Master Key Layer”. This is where your PMK (Pairwise Master Key) and GMK (Group Master Key) will be derived!
PMK (Pairwise Master Key)
The purpose of the PMK is to create seeding material for the PTK (pairewise transient key)
The PMK is derived by the station and authentication server (AAA). The PMK shall be computed as the first 256 bits (bits 0–255) of the MSK. Since the station and the authentication server (AAA) both have the same MSK, because of the 802.1X/EAP process, the PMKs derived will be identical.
The PMK that is derived at the authentication server (AAA) is sent to the authenticator. Once this occurs the station and authenticator both have identical PMKs. The PMK is unique between the station and the authenticator. No other station will have identical PMKs. A new PMK is generated when a station authenticates or re-authenticates . PMKs are also used in ‘fast’ roaming, whereby a client can negate a full 802.1X authentication. More about that in a future blog post. Again, keep in mind that the PMK is used as seeding material to create the PTK.
PSK - In the case where you use a PSK (PreShare Key) on a station and access point the Master Keys are derived by using a passphrase-to-PSK mapping. So your PSK is your PMK key.
Additional reading material
< IEEE Std 802.11 - 2007>
3.97 pairwise master key (PMK): The highest order key used within this standard. The PMK may be derived from a key generated by an Extensible Authentication Protocol (EAP) method or may be obtained directly from a preshared key (PSK).
< IEEE Std 802.11 - 2007>
The PTK shall not be used longer than the PMK lifetime as determined by the minimum of the PMK lifetime indicated by the AS, e.g., Session-Timeout + dot1xAuthTxPeriod or from the
dot11RSNAConfigPMKLifetime MIB variable. When RADIUS is used and the Session-Timeout attribute is not in the RADIUS Accept message, and if the key lifetime is not otherwise specified, then the PMK lifetime is infinite.
< IEEE Std 802.11 - 2007>
When not using a PSK, the PMK is derived from the MSK. The PMK shall be computed as the first 256 bits (bits 0–255) of the MSK: PMK L(MSK, 0, 256). When this derivation is used, the MSK must consist of at least 256 bits
< IEEE Std 802.11 - 2007> 5.8.2.2 Operations with PSK
The following AKM operations are carried out when the PMK is a PSK:
— A STA discovers the AP’s security policy through passively monitoring Beacon frames or through active probing (shown in Figure 5-11). A STA associates with an AP and negotiates a security
policy. The PMK is the PSK.
— The 4-Way Handshake using EAPOL-Key frames is used, just as with IEEE 802.1X authentication,
when an AS is present. See Figure 5-13.
— The GTK and GTK sequence number are sent from the Authenticator to the Supplicant just as in the
AS case. See Figure 5-13 and Figure 5-14.
GMK (Group Master Key)
The GMK is randomly created by the authenticator. The purpose of the GMK is to create “seeding material” for the GTK. The GMK lives on the authenticator ONLY. Each authenticator will have it’s own unique GMK. Some vendors allow you to change the GMK dynamically. I will share more on this in a future blog post.
“Temporal Key Layer”
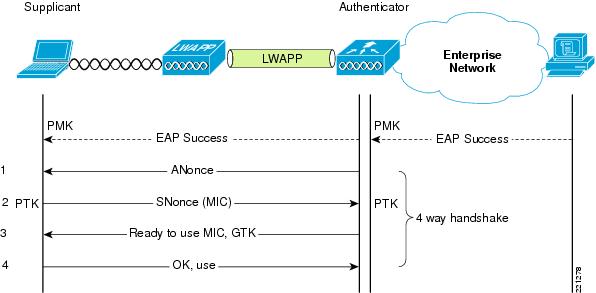
In the temporal key layer we will discuss two keys. The PTK (Pairwise Transient Key) and GTK (Group Temporal Key). Both have very unique tasks …. The temporal keys are derived via the 4-Way Handshake process.
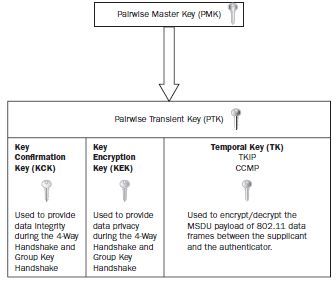
PTK (Pairwise Transient Key)
The propose of the PTK keys is to encrypt unicast traffic between the station and access point. The PTK is a unique encryption key and no other station will have the same identical PTK key.
The PTK is composed of 3 parts"
Key Confirmation Key (KCK), Key Encryption Key (KEK), Temporal Key (TK)
GTK (Group Temporal Key)
The purpose of the GTK key is to encrypt broadcast and multicast traffic between the client(s) and access point (BSS). ALL THE CLIENTS on the same BSS will share identical GTK keys. That right, multicast and broadcast traffic are keyed separate from the unicast traffic. Keeping in mind this is WHY when using a transitional network, your lowest encryption type is used for your GTK key.
You may have heard about the recent buzz in the industry around “hole 196”. This was based on the exploitation of the GTK key.
An important part of the PTK and GTK is the 4-way handshake. My next post will cover this in detail ..
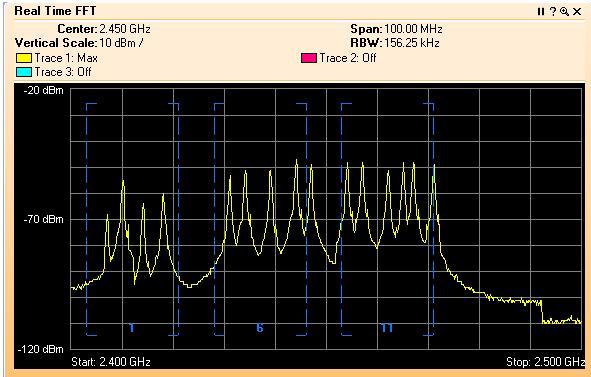
Great image of the frame exchange process
 Tuesday, November 8, 2011 at 4:37PM
Tuesday, November 8, 2011 at 4:37PM 
 George |
George |  Post a Comment |
Post a Comment |