GEORGE STEFANICK - CWSP JOURNEY, (CHAPTER 4 – EAP, EAP, EAP AND MORE EAP, POST#7)- 10/17/2010
 Sunday, October 17, 2010 at 3:47PM
Sunday, October 17, 2010 at 3:47PM Chapter 4 is one of my favorite chapters. Why you ask? It’s the very foundation to advance wireless security. EAP is the process where it all begins and comes together.
Have you ever talked to a vendor or colleague who is not familiar with EAP. You get that glazed look, as if you were from another planet? EAP is rather easy to understand once you know the structure. So lets cover the basics first.
WHAT EAP (IS) AND (IS NOT)
EAP stands for “Extensible Authentication Protocol”. EAP is an authentication frame work that has been around for a long long time.. What EAP is NOT is an authentication mechanism. There is often confusion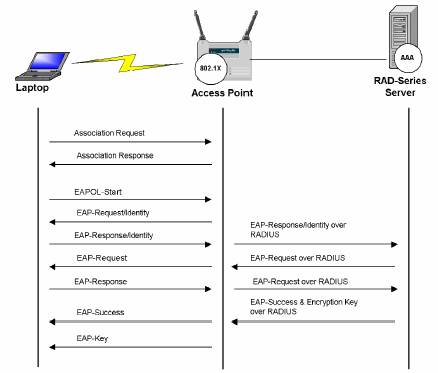 about this very statement. EAP doesn’t authenticate, but rather it provides the messaging system, the structure, for which authentication mechanisms like EAP-PEAP, EAP-TTLS, EAP-FAST, EAP-LEAP may operate.
about this very statement. EAP doesn’t authenticate, but rather it provides the messaging system, the structure, for which authentication mechanisms like EAP-PEAP, EAP-TTLS, EAP-FAST, EAP-LEAP may operate.
EAP was developed long ago, It was used primarily in point to point authentication (PPP). Whereby clients were authenticated to a network using an EAP authentication. Today, EAP is commonly used in wireless authentication and this will be the focus of my notes.
EAP is defined in RF3748 (http://tools.ietf.org/html/rfc3748). As I just shared it is the frame work or the message systems whereby different flavors of EAP can be used.
“Abstract
This document defines the Extensible Authentication Protocol (EAP),
an authentication framework which supports multiple authentication
methods. EAP typically runs directly over data link layers such as
Point-to-Point Protocol (PPP) or IEEE 802, without requiring IP. EAP
provides its own support for duplicate elimination and
retransmission, but is reliant on lower layer ordering guarantees.
Fragmentation is not supported within EAP itself; however, individual
EAP methods may support this.”
. Chapter 4 covers a rather broad range of information.
- · AAA (Authentication, Authorization, Accounting)
- · 802.1X Process and structure
- · Supplicant Credentials; types and uses
- · Authentication Protocols
- · EAP
My next few post will be the break down of each section …
 George |
George |  Post a Comment |
Post a Comment | 






Reader Comments