Cisco Security Response: Cisco Response to TKIP Encryption Weakness
 Friday, November 21, 2008 at 8:39PM
Friday, November 21, 2008 at 8:39PM Message Type : Security Response
Title: Cisco Security Response: Cisco Response to TKIP Encryption Weakness
URL: http://www.cisco.com/en/US/customer/products/products_security_response09186a0080a30036.html(available to registered users)
http://www.cisco.com/en/US/products/products_security_response09186a0080a30036.html
(available to non-registered users)
Posted: November 21, 2008
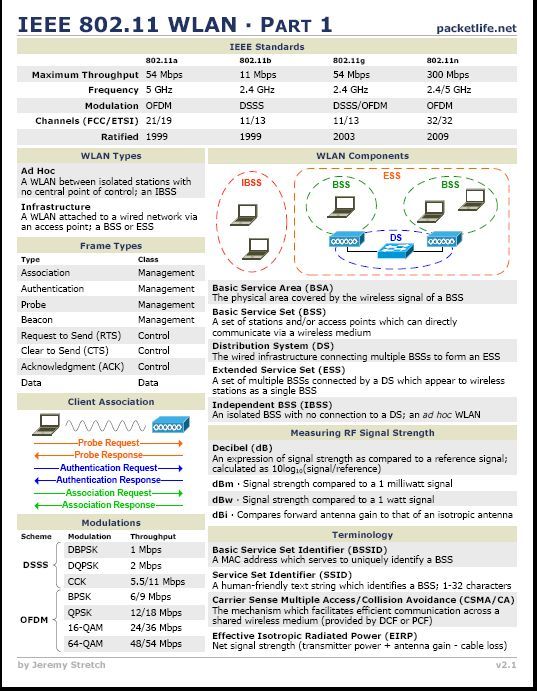
Summary: Several technology trade and other press outlets have recently released stories about security vulnerabilities in the Temporal Key Integrity Protocol (TKIP).
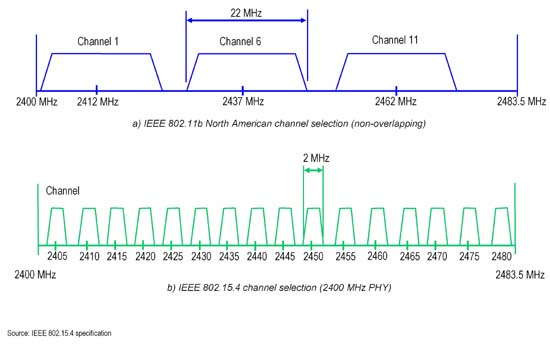
TKIP was developed after security vulnerabilities were found in the Wired Equivalency Protocol (WEP). This protocol was developed as a stopgap mechanism to address wireless security limitations in WEP for wireless devices that could not support the Advanced Encryption Standard (AES).
TKIP is the mandatory cipher suite for the first version of the Wi-Fi Protected Access
(WPA) specification and it is an option for the Wi-Fi Protected Access version 2 (WPA2)
standard.
 George |
George |  Post a Comment |
Post a Comment | 






Reader Comments